Data Loss Prevention Software
Unified Data Loss Prevention
Solution
Protect data across endpoints, SaaS apps, internet, email, and GenAI tools
from one unified platform. Enforce policies in real time with AI-powered
data classification and zero routing delays.
Kitecyber Data Shield: Unified Endpoint & Network DLP

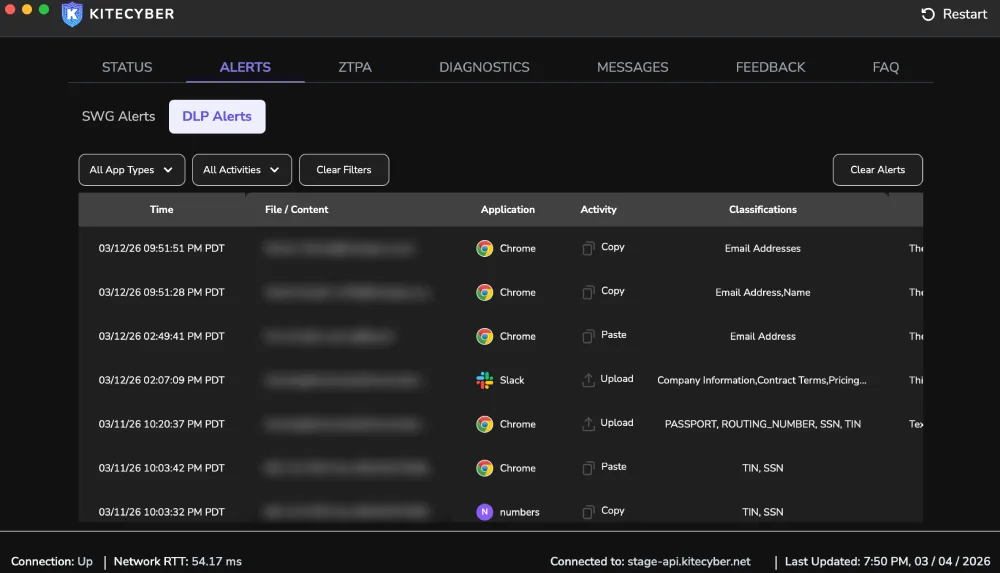
Detect & Manage Insider Theft

Deploy in minutes with zero-touch provisioning
Stop rogue uploads, Airdrop misuse, copy-paste exfiltration.
Struggling with data security?
“In-network DLP tools are too complex and expensive”
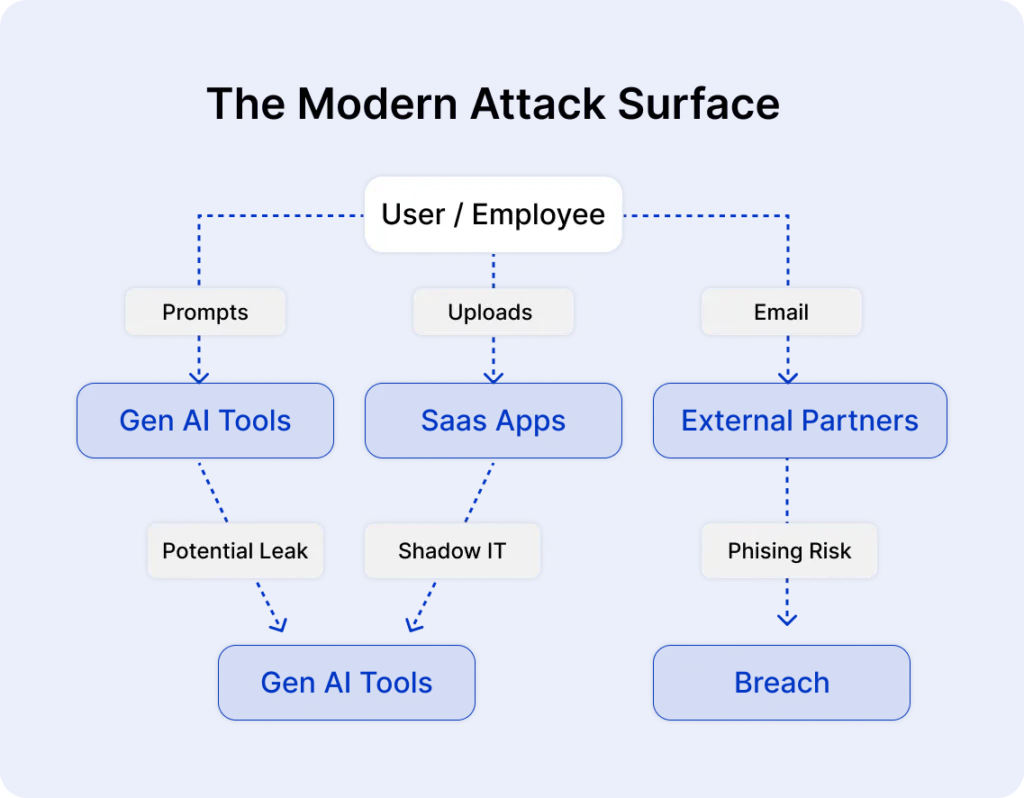
- Every prompt is a potential leak, and every endpoint is exposed.
You can solve it all with Kitecyber DLP
from a single policy engine.
- With Kitecyber
- Unified policy engine across endpoint, network, SaaS, email, and GenAI
- Endpoint-first enforcement that works anywhere, on any network
- Real-time GenAI prompt inspection before data leaves
- One agent, one console, deployed in days, not months
- Without Kitecyber
- Fragmented tools across endpoint, network, SaaS, and email
- No visibility into GenAI tools like ChatGPT or Copilot
- No protection for remote workers off the corporate network
- Months of deployment, constant tuning, and alert fatigue
Product Overview
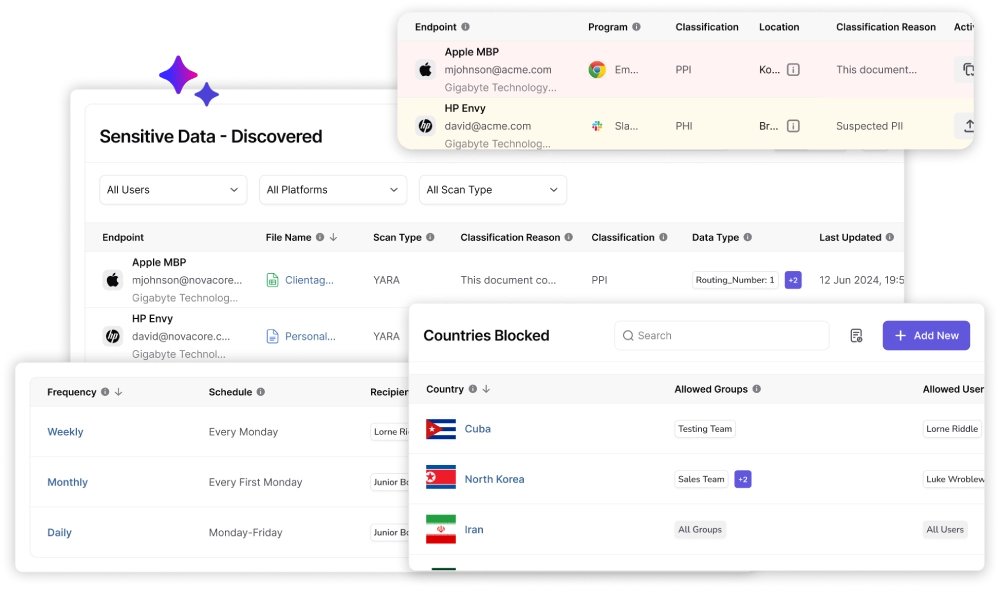
DLP that works where your data actually lives
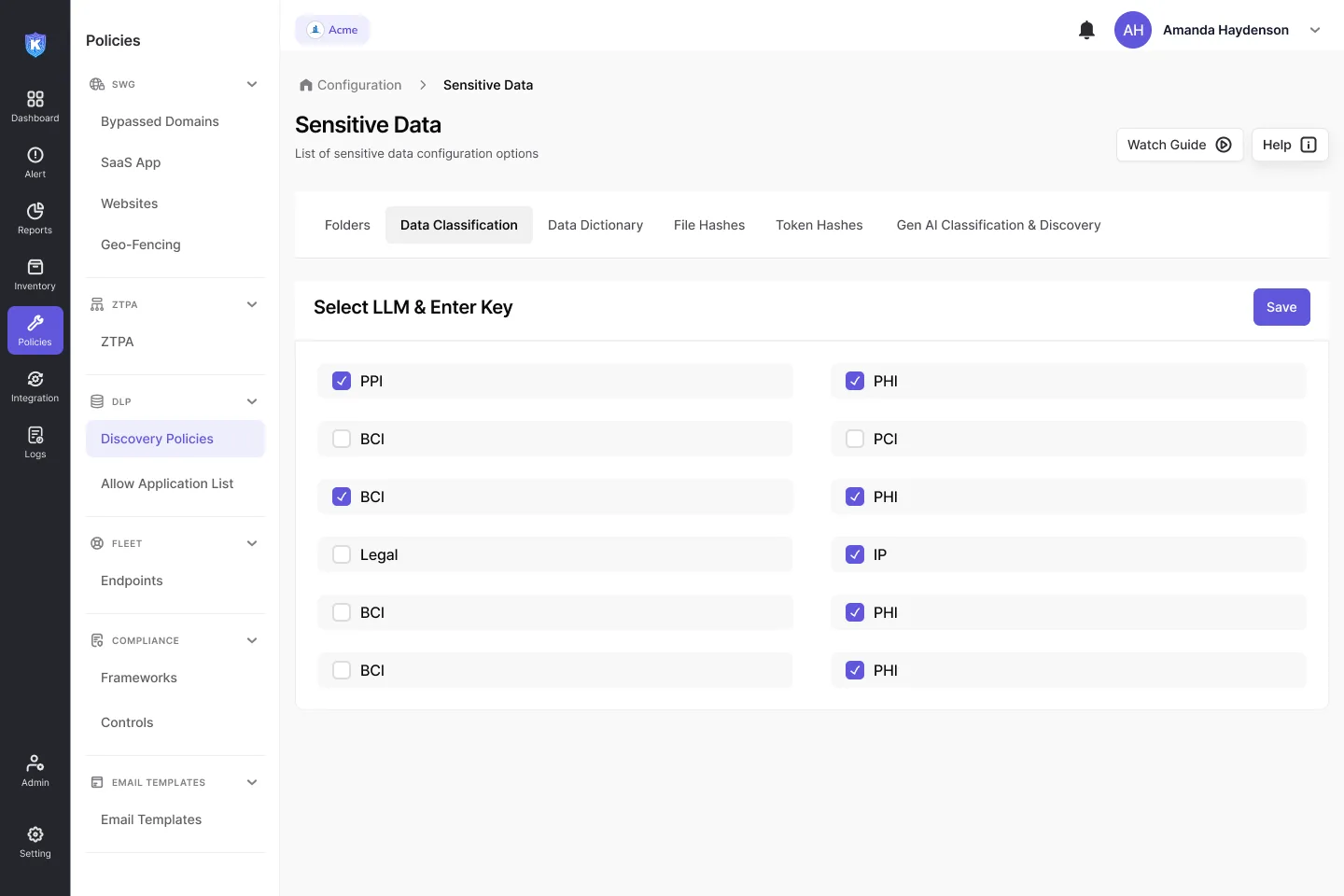
GenAI-powered classification with real context
Kitecyber uses contextual AI, not just regex or OCR, to achieve over 90% accuracy. This reduces false positives and ensures continuous protection across data at rest, in use, and in motion.
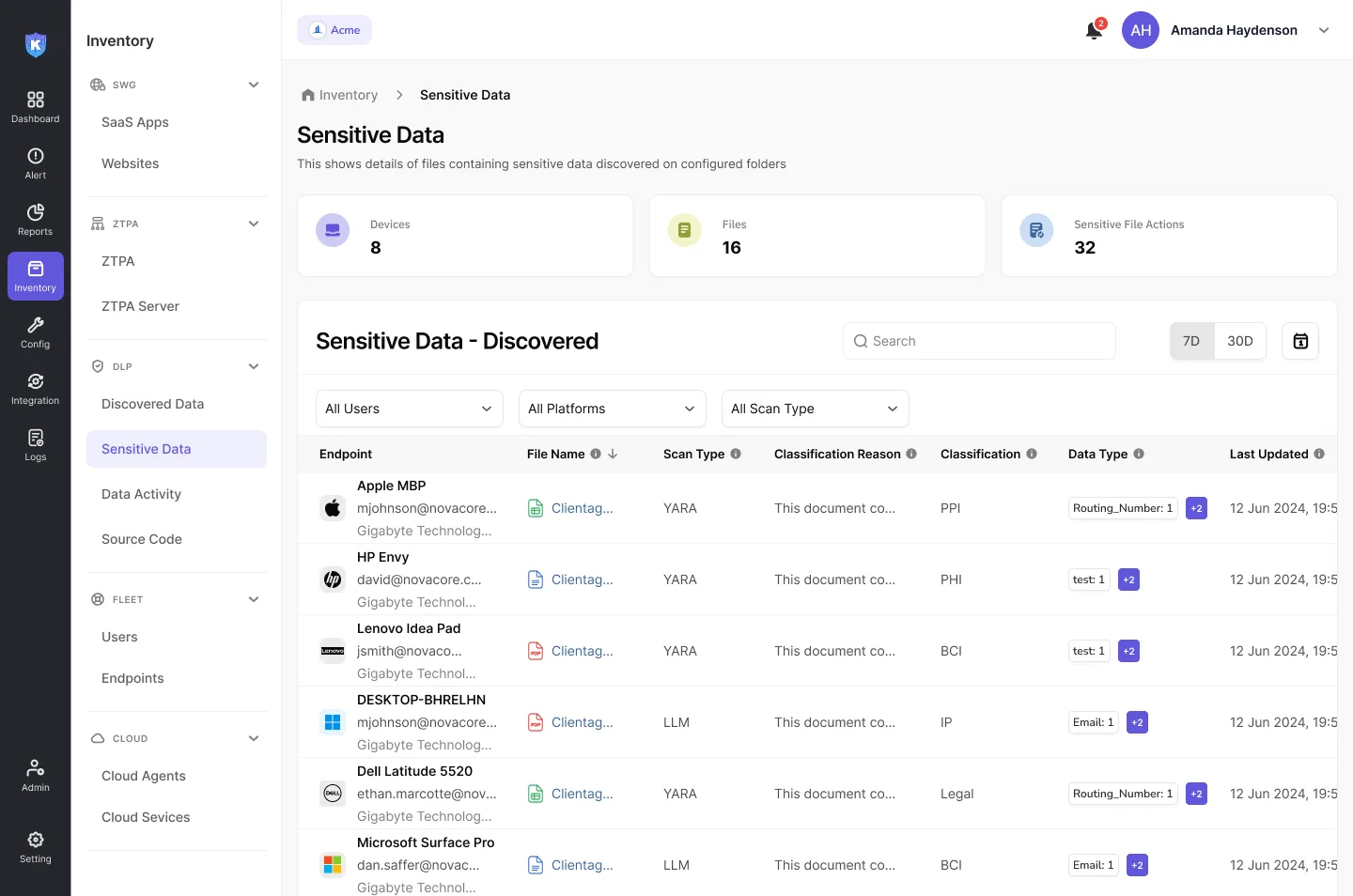
Find and protect data on business devices
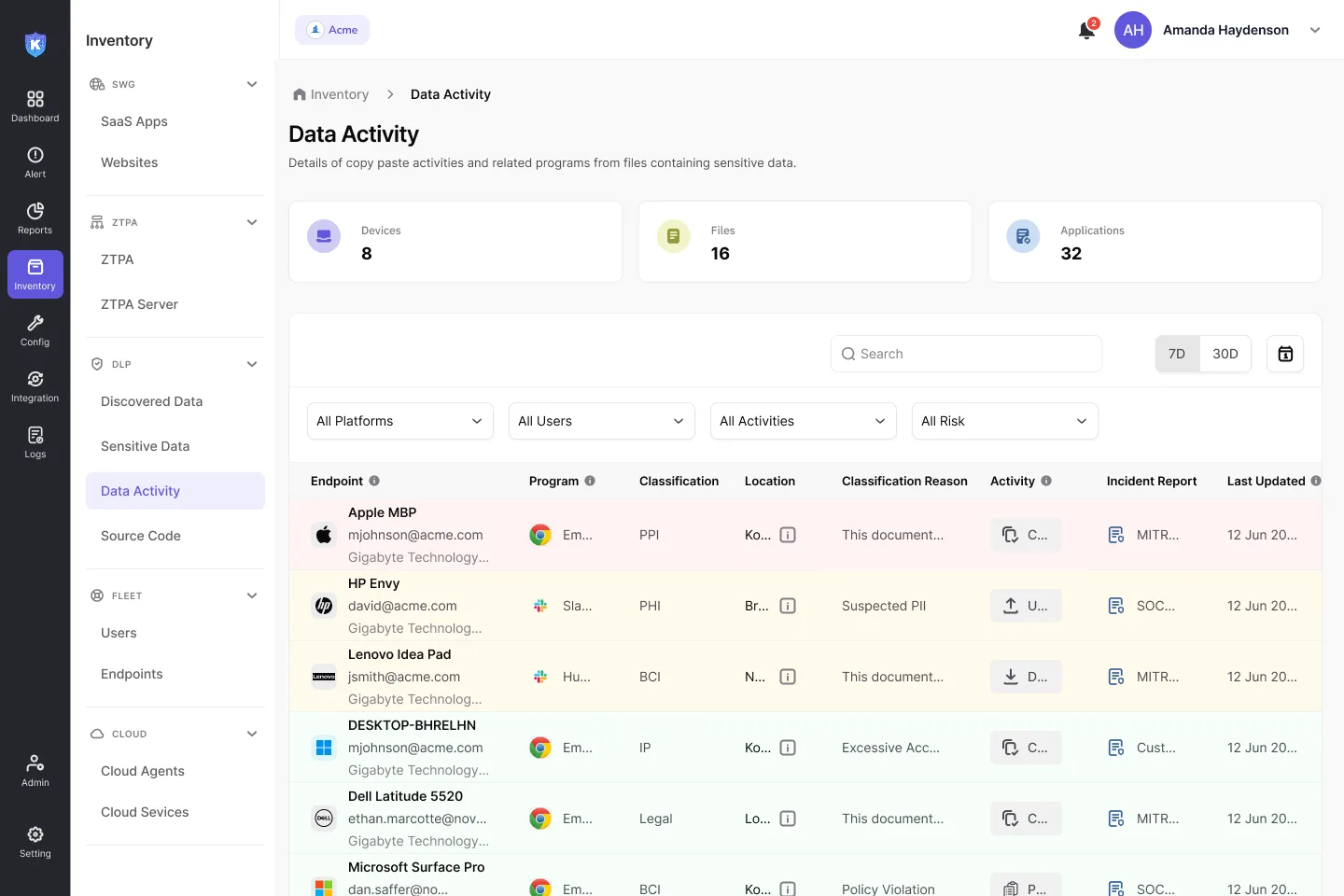
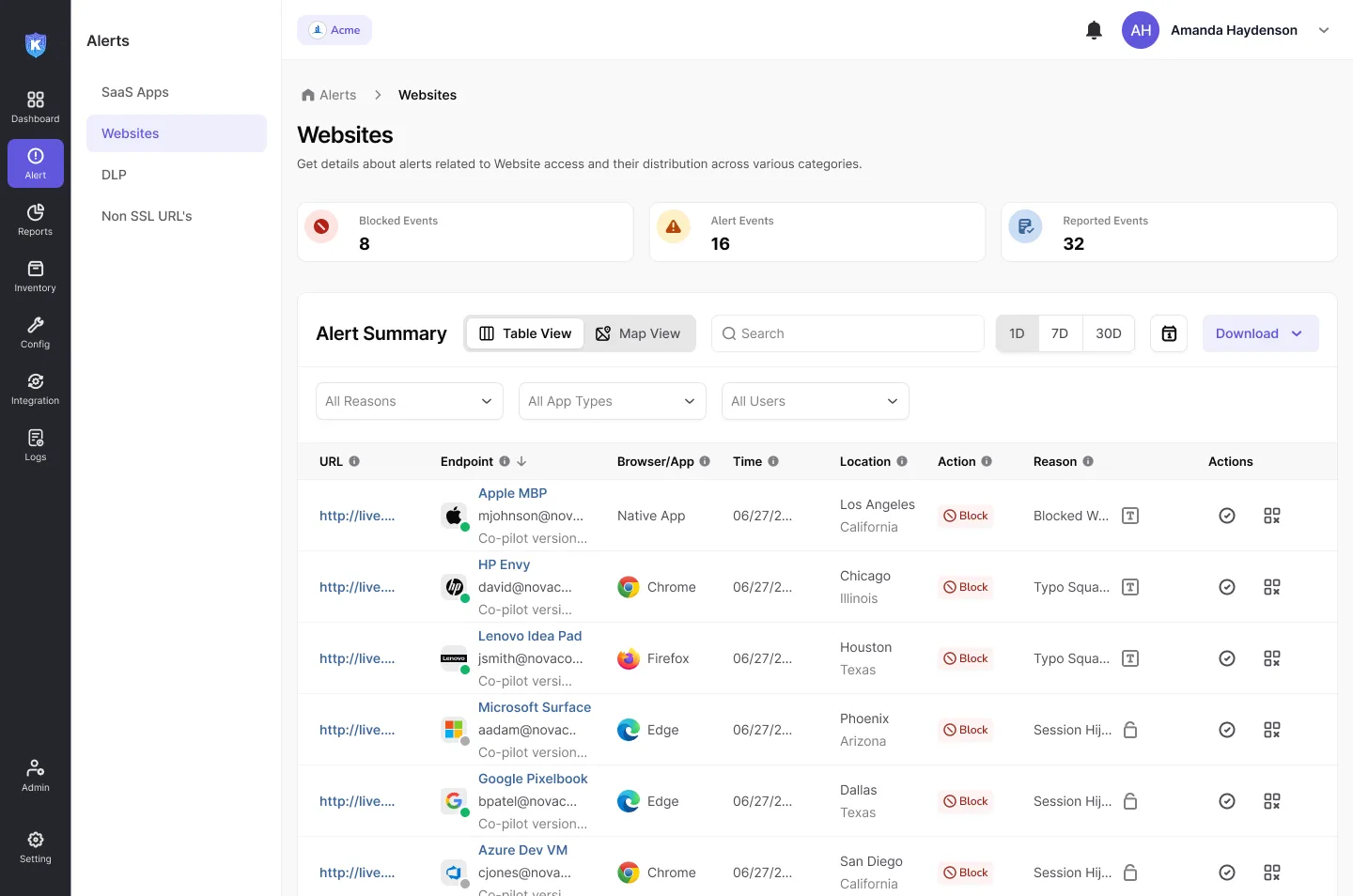
Stop data exfiltration before it happens
Kitecyber enforces consistent controls across every data movement channel: internet, SaaS/ Gen AI Apps, and devices. Monitor and block security incidents in real time wherever users interact with data intentionally or unintentionally.
Coverage includes:
Endpoint – USB, copy/paste, screenshots, shares
Email – attachments, inline copy-paste, misdirected sends
SaaS & GenAI – uploads, downloads, prompts
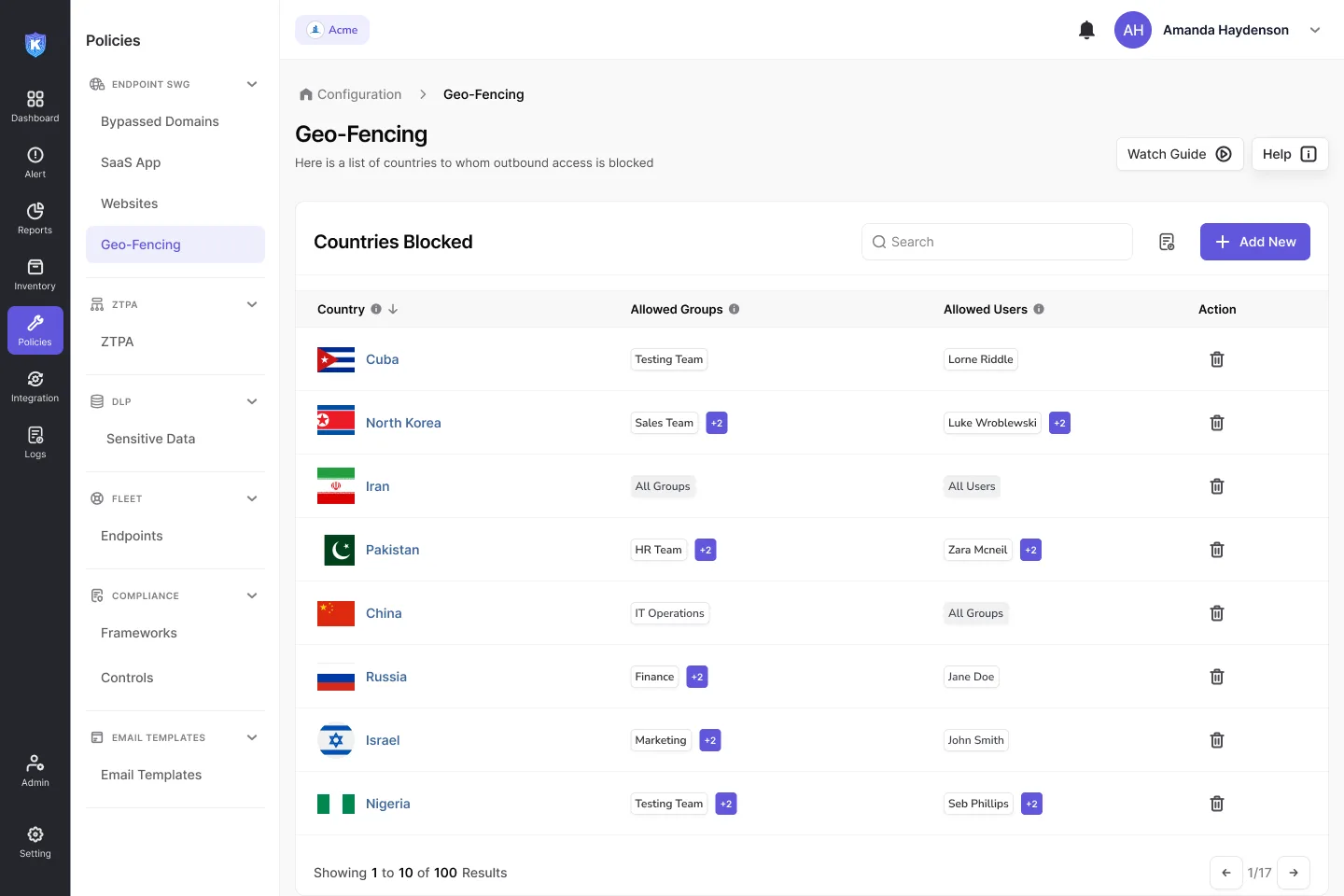
Network – Website/ Application Blocking, Geofencing
AI-powered defense for safer browsing
Secure access based on location
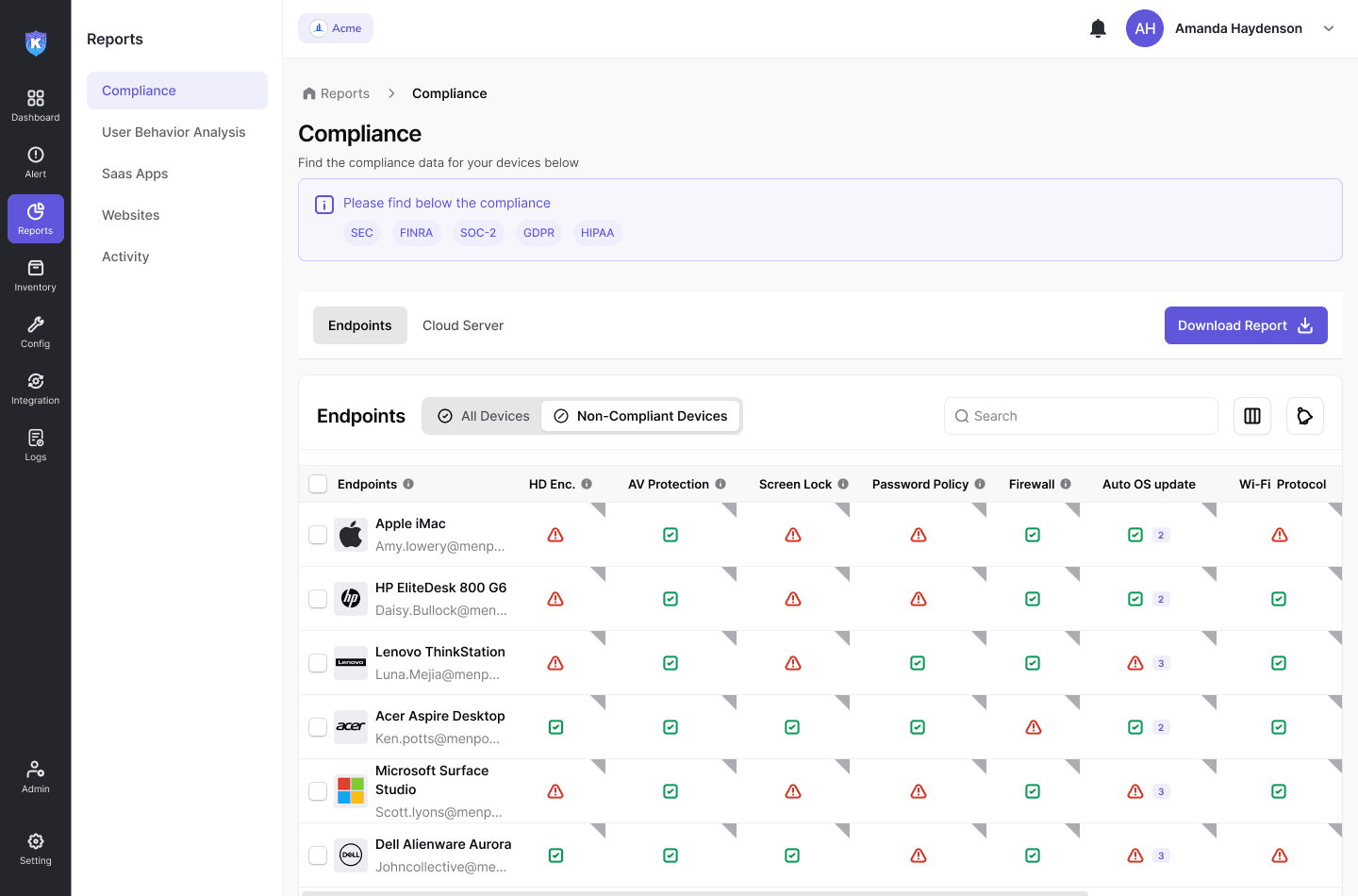
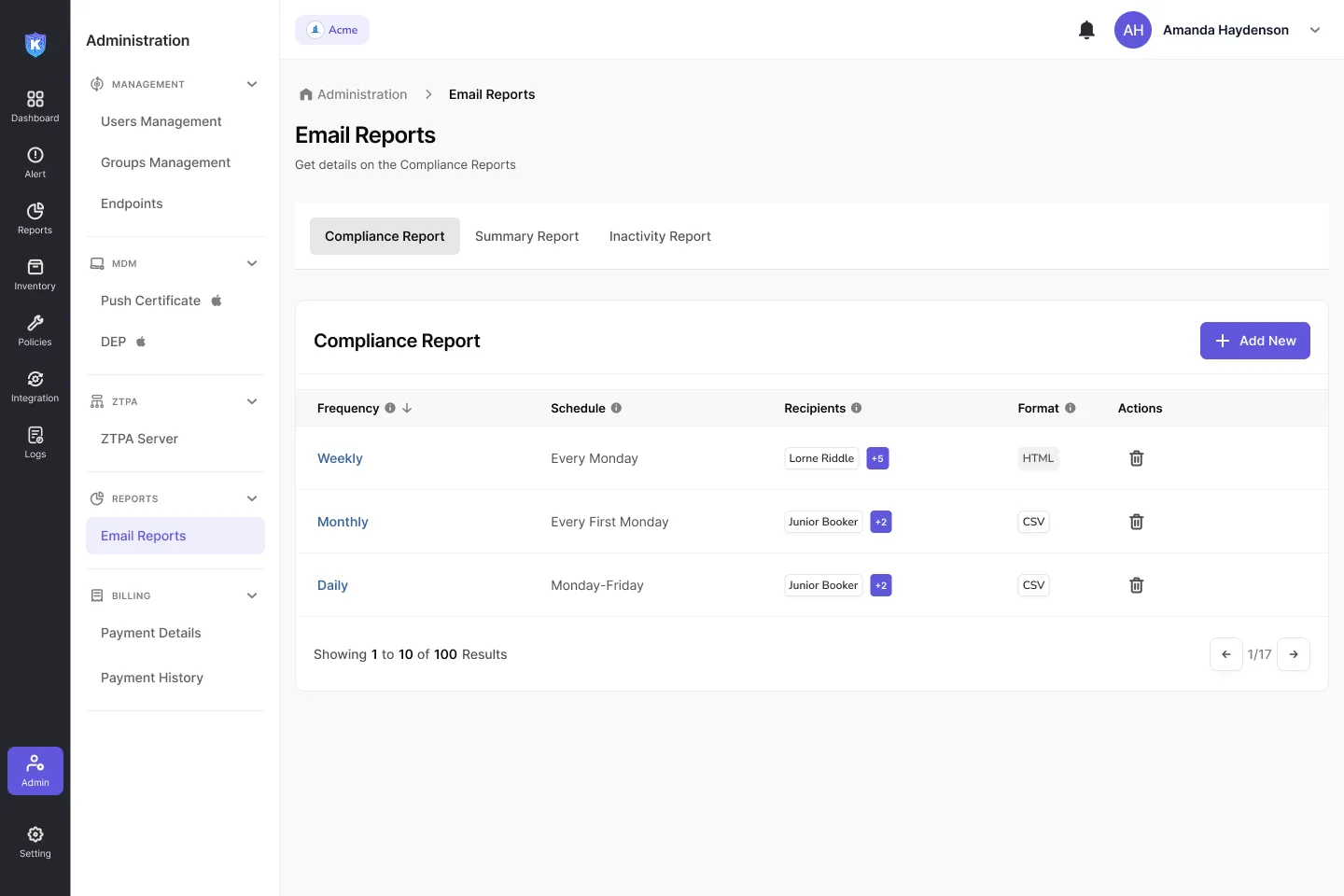
Enforce policies and stay compliant
Audit-ready reporting with full visibility
Build strong data hygiene across your workforce
With risk-driven insights, the Kitecyber DLP agent runs on every endpoint to monitor activity, coach better decisions in the moment, and reinforce secure behavior. Over time, this creates lasting data hygiene without slowing your teams down.
The numbers
-90%
False Positives
30%
Reduction in compliance prep time
4x
More data surfaces covered vs legacy tools
1 Day
Deployment, not months
Why Kitecyber over traditional DLP tools
See how we stack up against other dlp softwares in the market. We built KiteCyber for speed, accuracy, and modern workflows.
Incident Response
Minutes to generate reports vs. Weeks for traditional forensics.
User Experience
<2% CPU overhead vs. Heavy scans causing spikes.
False Positive Rates
Low (AI-driven context) vs. High (Regex/OCR).
Incident Response
Minutes to generate reports vs. Weeks for traditional forensics.
User Experience
<2% CPU overhead vs. Heavy scans causing spikes.
False Positive Rates
Low (AI-driven context) vs. High (Regex/OCR).
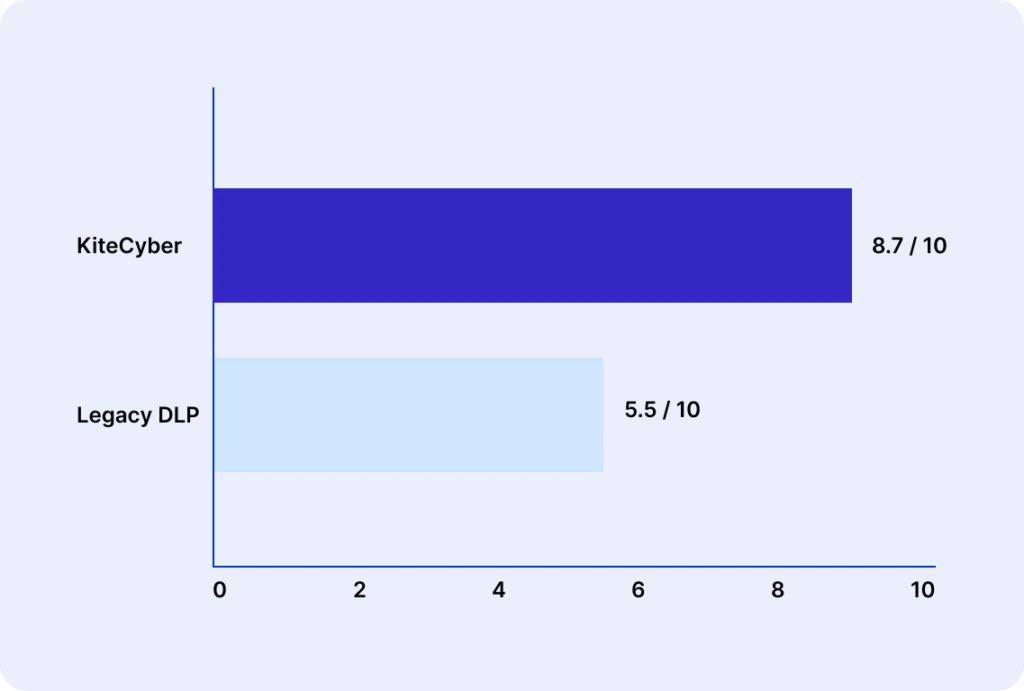
Kitecyber vs Traditional DLP Solutions
| Feature / Capability | Kitecyber DLP | Traditional DLP |
|---|---|---|
G2 Ease of Use |
Simple (8.7 / 10) | Complex |
Insider Threats |
ComprehensiveEncrypted app & data, Offline monitoring, Password-protected file tracking |
Limited offline endpoint enforcement |
Incident Response & MITRE ATT&CK Reports | Minutes to generate; 150+ behavior indicators; Advanced forensics | Weeks to months of forensics and correlation |
Ransomware Protection | ComprehensiveC2/IP blocking, Supply-chain API monitoring, Managed disk encryption; Mitigates ~80% techniques in MITRE tests; Incident response in minutes | IPS & anti-evasion sandboxing; Remote browser isolation; Weeks to months of forensics |
False Positive Rates | LowAI-driven detection, Minimal tuning, Contextual awareness | HighTraditional OCR detection, Extensive policy refinement |
User Experience | Excellent<2% CPU overhead, Zero network impact, Transparent UI | PoorHeavy scans, CPU/memory spikes, Complex tuning |
Deployment Model | No appliances or cloud gateways; Single endpoint agent; Cloud-native management | Agent, appliance, or cloud gateway; Management server & gateways with complex topology |
DLP Solution | Universal agent includes Endpoint DLP with USB and network share controls; Network & Cloud DLP with GenAI & SaaS app controls; Real-time blocking in SaaS apps | Siloed solutionNo appliances or cloud gateways; Single endpoint agent; Cloud-native management |
Data Lineage & Discovery | ComprehensiveCross-platform audit trails, AI classification, Real-time alerts | PartialEDR, Endpoint DLP, CASB, DSPM with data mesh & analytics tools; Weak real-time protection |
Location-Aware Security | ComprehensiveGeo-fencing policies by region, Dynamic peripheral control (e.g., camera disable) on-premises | PoorDevice control limited to removable storage; No camera disable or geolocation enforcement |
The Kitecyber Advantage
- Before Kitecyber Data Shield
- In-network DLPs only detect what they’re programmed for, leaving real risks like agentic AI apps and insider threats unnoticed.
- IT waits for about 2 months to deploy hard-to-configure DNS rules, which frustrates employees
- In-network DLPs leave scanning all file types and ignore files of bigger size.
- After Kitecyber Data Shield
- Kitecyber DLP runs on your endpoint with an agent, adapts to users behaviour, and detects all shadow AI, supply chain apps, and insider actions.
- IT starts tracking sensitive data movement in a few days after copilot deployment.
- Kitecyber Data Shield scan files of all types and sizes
Use-case
Ensure Data security and Compliance Without Slowing Teams
Ransomware Protection
Safeguard against malicious links & data exfiltration
Insider Threat Mitigation
Continuous monitoring and enforcement.
Edge Data Leak Prevention
Control SaaS, Gen AI sprawl, and endpoint sharing.
UEBA-Powered Exfiltration Prevention
Detects and blocks anomalous data activity.
Streamlined Compliance
GDPR, HIPAA , PCI ‑DSS, ISO 27001, and more.
Maximizing Data Visibility and Compliance for a Growing Financial Firm
Our Success Stories
Testimonials

“Kitecyber has been a game changer for our IT and security teams. Now they don’t operate in silos and can see a unified dashboard. We feel much better in our security posture and are saving almost 20 hrs a week in dealing with issues and tickets related to previous solutions. We also saved 50% in our total cost of ownership.”

“Kitecyber helped us with IT, security and compliance as a unified solution. It saved us almost 50% in overall cost as compared to our previous solutions, while significantly improving our security and compliance. the builtin device management and IAM integrations, also optimized our onboarding and offboarding workflows.”

“Kitecyber has been amazing for our SMB customers, who can now enjoy enterprise grade security with a simple and cost effective solution. Instead of dealing with multiple complex solutions, with Kitecyber they can get advanced security with ease using a single copilot”

“No single product prior to Kitecyber could meet so many of the compliance controls while providing advanced SSE protection to SMBs. We are glad to partner with them and integrate with our GRC solution to simplify SMB security and compliance.”

"After being scammed online, we decided to use Kitecyber and it has been awesome to find such a simple and effective security solution with so much coverage. One of the best solutions if you have remote teams who need protection and you need better sleep."
Awards & Recognitions

"Robust and reliable cybersecurity platform for device management, secure browsing and VPN"
Kitecyber stood out as a single product that is able to replace multiple point solutions. It was very easy to install even without having any secur...
Read More >>

"Lightweight, Powerful, and Built for Modern Teams to make Endpoint Security Surprisingly Simple"
We've been using KiteCyber for several months now, and it has quickly become a cornerstone of our security stack. The standout benefit is how effor...
Read More >>

"Intuitive yet robust security software"
KitCyber has been extremely simple for us to install for end point security. The built in device management and custom security rules for users has been extremely useful. In addition to protecting from...
Read More >>

"Effective and User-Friendly Cybersecurity Monitoring Platform"
The platform is easy to navigate, with clean dashboards and intuitive workflows. It provides timely threat insights and helps us track incidents efficiently. The customer support team is responsive...
Read More >>

"Easy- Single platform for all IT Security and compliance"
We've had a great experience with KiteCyber — it's a truly user-friendly platform that made onboarding incredibly smooth. The setup process was impressively quick, taking less than an hour...
Read More >>

"ZTNA, URL/App Controls & MDM - all in one"
We’ve been using the platform for ZTNA, URL/App controls, and MDM, and it’s been a smooth experience. It’s feature-rich but easy to use, which made setup and daily management...
Read More >>

"Reliable and Efficient Cybersecurity Partner"
KiteCyber offers an intuitive, well-organized platform that simplifies cybersecurity monitoring and compliance management. The dashboards provide clear visibility into security posture,...
Read More >>

"Hit ESC (Easy. Secure and Cost-effective) key to security gaps, complex and siloed security tools"
Kitecyber gives us a single, easy-to-use dashboard to protect our devices, apps, data, and...
Read More >>

""Best MDM (and much more) for small business and SMBs.""
Product is phenomenal. Price is incredible. The best thing though is how easy their team makes it...
Read More >>

"Top notch team and cybersecurity platform"
What do you like best about Kitecyber?
They have a robust platform, unique in the market. Their.....
Read More >>

"Great MDM, SWG and ZTNA product"
We were looking for security products to cover our need for device management, compliance controls, SaaS security and VPN to cloud...
Read More >>

"Cyber Security plus Remote Team’s Management Support SaaS"
Post experiencing a scam, we went ahead with enrolling KiteCyber and Not only it prevents our database from scammers and hackers...
Read More >>

"Wonderful Application"
What do you like best about Kitecyber?
It is a mix of Jumpcloud and ZTNA application
What do you dislike about Kitecyber?
It blocks unsafe...
Read More >>

"Great endpoint and network security tool"
What do you like best about Kitecyber?
It works very well with GRC solutions like Scrut and make it easy for customers to get security and compliance...
Read More >>

"Great solution to manage devices, team and complaince"
What do you like best about Kitecyber?
It helped me see all the devices in the company, both allocated and unallocated...
Read More >>

"Best cybersecurity product"
What do you like best about Kitecyber?
Identify cyber threats and zero trust vpn connection..The product is very helpful to understand and identify cyber threats..
Read More >>