Table Of Content
Best Patch Management Software and Tools for 2026
-
April 16, 2026
-
Summary: DLP solutions (Data Loss Prevention solutions) protect sensitive data from unauthorized access, transfer, or exposure across endpoints, cloud apps, and AI tools. Modern DLP tools like Kitecyber, Microsoft Purview, and Nightfall AI use AI and data lineage to track how data moves, reducing false positives by over 90% compared to legacy systems. The best 2025 DLP solutions combine content and context awareness, protecting data across SaaS platforms, endpoints, and generative AI environments.
In 2024 alone, 40,294 vulnerabilities were disclosed, and 2025 has already crossed the 5,000 mark. As the digital workforce expands and attack surfaces grow, the volume of risk is no longer manageable through manual processes.
That shift is pushing admins toward automated patch management.
Patch Management automation does more than reduce repetitive workload. It cuts down hours spent on routine patching while ensuring critical and zero-day updates are deployed without delay. The result is faster remediation, tighter control, and far less exposure to known threats. Ransomware groups like LockBit and BlackCat routinely exploit CVEs within 48 hours of public disclosure.
That gap between patch release and patch deployment is where breaches happen. It is not a technical problem. It is an operational one. Most organizations already have patch management tools. What they lack is consistency, visibility, and automation across every endpoint, including remote laptops, cloud workloads, and third-party applications.
Patch Management Software is the infrastructure layer that closes that gap. This guide covers everything you need to know: how it works, what capabilities matter, which tools lead the market, and how to choose the best patch management software for your environment.
That shift is pushing admins toward automated patch management.
Patch Management automation does more than reduce repetitive workload. It cuts down hours spent on routine patching while ensuring critical and zero-day updates are deployed without delay. The result is faster remediation, tighter control, and far less exposure to known threats. Ransomware groups like LockBit and BlackCat routinely exploit CVEs within 48 hours of public disclosure.
That gap between patch release and patch deployment is where breaches happen. It is not a technical problem. It is an operational one. Most organizations already have patch management tools. What they lack is consistency, visibility, and automation across every endpoint, including remote laptops, cloud workloads, and third-party applications.
Patch Management Software is the infrastructure layer that closes that gap. This guide covers everything you need to know: how it works, what capabilities matter, which tools lead the market, and how to choose the best patch management software for your environment.
The Modern Patching Problem
Endpoints Are Everywhere and Growing
The average enterprise now manages 135,000 endpoints. Remote work has pushed thousands of devices outside the corporate perimeter. Mobile devices, home routers, VPN clients, and unmanaged personal machines create a patching surface that traditional tools were never designed to handle.
IT teams that once patched servers in a controlled data center now face hundreds of OS variants, dozens of third-party applications per device, and a workforce that resists restarts and update prompts.
IT teams that once patched servers in a controlled data center now face hundreds of OS variants, dozens of third-party applications per device, and a workforce that resists restarts and update prompts.
Third-Party Applications Are the Weakest Link
Operating system patches get most of the attention. But third-party applications, Chrome, Zoom, Adobe Reader, Slack, Java, Python runtimes, represent a larger and faster-growing attack surface. According to Secunia Research, third-party application vulnerabilities account for more than 83% of vulnerabilities on a typical Windows endpoint.
Traditional patch management tools often cover OS updates well and third-party applications poorly. Attackers know this. They target the gaps.
Traditional patch management tools often cover OS updates well and third-party applications poorly. Attackers know this. They target the gaps.
Patch Delays Are an Operational Problem, Not Just a Technical One
Most organizations prioritize patches by severity rating alone. They run patching cycles on monthly cadences. They depend on manual approval workflows. The result is a backlog of hundreds of open vulnerabilities per endpoint, with the most dangerous ones buried under noise.
When a zero-day drops, a 30-day patching cadence becomes a 30-day exposure window.
When a zero-day drops, a 30-day patching cadence becomes a 30-day exposure window.
What Is Patch Management Software?
Patch Management Software is a category of security and IT operations tools that automate the discovery, testing, deployment, and verification of software updates across endpoints, servers, and cloud workloads. It continuously monitors the environment for missing patches, maps them to known vulnerabilities, prioritizes remediation by risk level, and deploys updates without requiring manual intervention at scale.
Modern patch management platforms extend beyond OS updates to cover third-party applications, firmware, browsers, and productivity tools across Windows, macOS, and Linux environments.
Modern patch management platforms extend beyond OS updates to cover third-party applications, firmware, browsers, and productivity tools across Windows, macOS, and Linux environments.
Why Patch Management Matters
Reduce Attack Surface
Every unpatched vulnerability is an open door. Patch management systematically narrows the number of exploitable entry points across your environment. A mature program can reduce your exploitable attack surface by more than 70% within the first 90 days.
Prevent Ransomware and Exploit-Based Attacks
The majority of ransomware campaigns begin with exploitation of a known, patchable vulnerability. WannaCry exploited EternalBlue, a vulnerability patched two months before the outbreak. NotPetya used the same vector. Cl0p ransomware spent 2023 exploiting an unpatched MOVEit file transfer vulnerability. The pattern repeats because delayed patching remains common.
Meet Compliance Requirements
PCI DSS 4.0 requires critical patches within 30 days of release. HIPAA mandates risk management that includes timely remediation of known vulnerabilities. NIST SP 800-40 provides the foundational framework for patch management as a security control. ISO 27001, SOC 2, and CIS Controls all include patching requirements. Patch management software generates the audit trails and compliance reports these frameworks require.
How Patch Management Works
A modern patch management workflow runs in five stages:
- 1. Vulnerability Detection The agent scans each endpoint continuously and maps installed software versions against CVE databases, vendor advisories, and threat intelligence feeds to identify which systems are missing which patches.
- 2. Patch Identification The platform cross-references detected vulnerabilities with available patches from vendors, validates their authenticity, and stages them for deployment.
- 3. Testing and Approval Patches are tested against a pilot group before broad rollout to catch compatibility issues. Policy-based approval workflows allow security teams to set auto-approval thresholds for low-risk patches and require manual review for critical system updates.
- 4. Deployment The platform pushes patches to endpoints based on defined schedules, user activity patterns, and bandwidth constraints. Remote devices are handled through cloud-native delivery without requiring VPN connectivity.
- 5. Reporting and Verification Post-deployment scans confirm successful installation, flag failures, and generate compliance reports that map patch coverage to specific CVEs and regulatory requirements.
Types of Patch Management
|
Type |
What It Covers |
| OS Patching | Windows, macOS, Linux kernel and system updates |
| Third-Party App Patching | Chrome, Zoom, Adobe, Java, Python, Slack, and 500+ applications |
| Endpoint Patching | Laptops, desktops, mobile devices, virtual machines |
| Cloud Workload Patching | EC2, Azure VMs, GCP instances, containerized workloads |
| Firmware Patching | BIOS, drivers, network interface firmware |
Core Capabilities of Patch Management Software
- Automated Patch Deployment Policy-driven patching removes manual steps from routine updates. Set rules once. The platform executes them across thousands of endpoints without IT intervention.
- Vulnerability Scanning Continuous scanning provides real-time visibility into patch gaps. Dashboards show open CVEs, severity levels, affected device counts, and time-to-remediation.
- Patch Prioritization Not all patches are equal. Modern tools prioritize based on CVSS score, exploitability in the wild, asset criticality, and active threat intelligence.
- Scheduling and Rollback Deploy patches during maintenance windows to minimize disruption. Rollback capabilities let teams revert a patch that causes application compatibility issues without manual re-imaging.
- Compliance Reporting Pre-built reports map your patch coverage to PCI DSS, HIPAA, CIS, NIST, and SOC 2 requirements. Export-ready formats support audit submissions.
Advanced Capabilities (The Ones That Separate Good Tools from Great Ones)
Risk-Based Patching
Severity ratings alone do not reflect actual risk. A CVSS 7.5 vulnerability being actively exploited in ransomware campaigns is more urgent than a CVSS 9.0 vulnerability with no known public exploit. Risk-based patching factors in exploit availability, threat actor activity, asset exposure, and business context to rank remediation priority.
CVE Prioritization with Threat Intelligence
Integration with CISA KEV (Known Exploited Vulnerabilities), NVD, and commercial threat feeds lets the platform flag CVEs that attackers are actively targeting in the wild, so your team remediates the right vulnerabilities first.
Zero-Day Response Workflows
When a zero-day drops, standard patching cadences are too slow. Purpose-built workflows trigger immediate scans, identify all exposed assets, and initiate emergency deployment cycles within minutes of a patch becoming available.
Cross-OS Support
Modern enterprise environments run Windows, macOS, and Linux simultaneously. Cross-OS patching eliminates the need for separate tools and ensures no platform becomes a blind spot.
Remote Device Patching
Cloud-native agent architecture patches remote devices without VPN dependency. Laptops in coffee shops, home offices, and airport lounges receive patches on the same schedule as on-premises devices.
Integration with Security Tools
Bidirectional integration with SIEM platforms, vulnerability management tools, ITSM systems, and EDR solutions creates a unified view of risk and response. Patch status feeds into broader security workflows rather than living in a separate silo.
Automation and Policy-Based Enforcement
Define patching policies by device group, OS, application category, risk level, or business unit. Enforce them automatically. Eliminate patching inconsistency across distributed teams.
Benefits of Modern Patch Management
- Reduced Risk Exposure Systematic patching shrinks the window between vulnerability disclosure and remediation from weeks to hours. Fewer open CVEs mean fewer exploitable paths into your environment.
- Faster Remediation Automation removes the manual effort of identifying, downloading, testing, and deploying patches at scale. Teams that spent 40+ hours per week on patching operations routinely recover significant capacity.
- Lower Operational Overhead Consolidated visibility across OS and third-party patching reduces the tool sprawl that creates coverage gaps. One platform, one dashboard, one compliance report.
- Improved Compliance Posture Continuous patch coverage and automated reporting make compliance audits faster, cheaper, and less disruptive. Evidence of patching activity is available on demand.
Why Traditional Patching Fails
- Manual Processes Cannot Scale Manually reviewing, approving, and deploying patches for thousands of endpoints across dozens of OS versions and hundreds of applications is not operationally viable. Manual patching accumulates debt faster than it resolves it.
- Lack of Visibility Across the Environment Most organizations lack a unified view of patch status across all endpoints, especially remote devices and unmanaged assets. What you cannot see, you cannot patch.
- Inconsistent Deployment Monthly patch cycles, device downtime, user resistance to restarts, and network bandwidth limitations cause inconsistent patch coverage. Partial deployment creates a false sense of security.
- Remote Workforce Challenges Traditional patch management tools were built for on-premises environments. Remote devices on home networks may go weeks without connecting to corporate infrastructure, leaving them perpetually behind on critical updates.
12 Best Patch Management Software in 2026
Paid Patch Management Tools
1. Kitecyber Patch Management

Kitecyber takes an endpoint-first approach, combining vulnerability detection, automated patching, and security posture management in a single cloud-native platform. It covers Windows, macOS, and Linux with broad third-party application support. Its risk-based prioritization engine uses active threat intelligence to surface the patches that matter most. Remote device support is built into the architecture, not bolted on.
2. Microsoft Intune

Intune provides strong OS patch management for Windows-centric environments and integrates tightly with the Microsoft 365 ecosystem. Third-party application patching coverage is limited compared to dedicated patch management platforms. Best suited for organizations already standardized on Microsoft infrastructure.
3. ManageEngine Patch Manager Plus

A feature-rich platform with broad OS and third-party application support. Offers agent-based deployment, patch testing workflows, and compliance reporting. The interface can feel complex for teams new to enterprise patch management. Strong choice for mid-market IT teams managing heterogeneous environments.
4. Automox
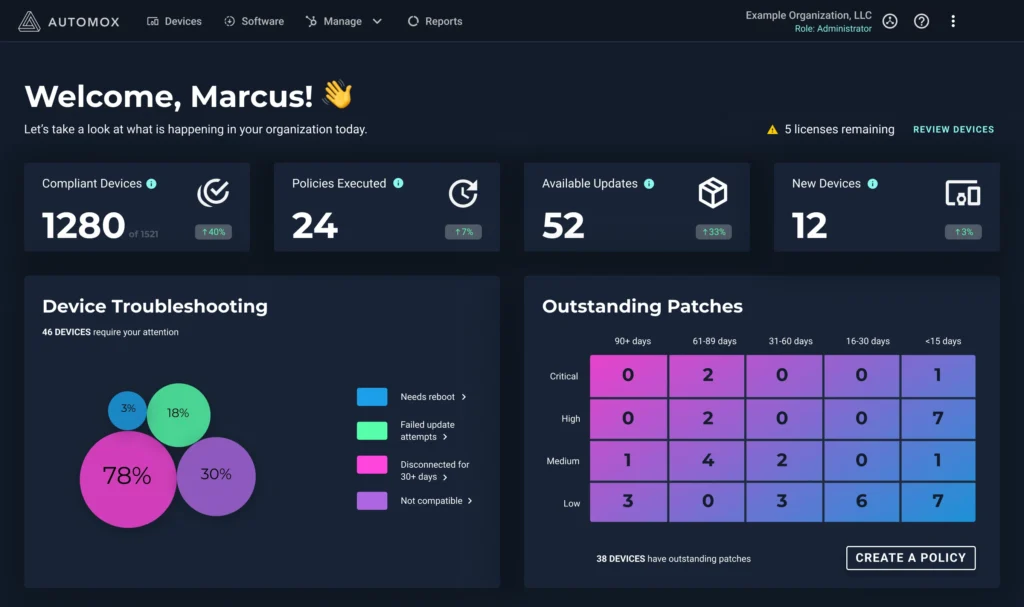
Cloud-native patch management with good cross-OS support. Its policy-based automation and remote patching capabilities suit distributed workforces. The platform’s API-first design supports integration with existing security stacks. Pricing scales with device count.
5. Ivanti Patch Management

Ivanti offers enterprise-grade patching with deep integration into its broader IT service management suite. Strong compliance reporting and risk-based patching capabilities. Better suited for organizations that want patch management as part of a broader ITAM or ITSM platform.
6. NinjaOne

Popular among managed service providers for its ease of use and multi-tenant architecture. NinjaOne combines patch management with RMM capabilities. Third-party patching coverage is solid. Reporting depth is competitive. Good fit for IT teams managing multiple client environments.
7. Atera

An all-in-one RMM and PSA platform targeting IT departments and MSPs. Atera offers automated patch management with AI-driven alerts. Its flat-rate pricing model is appealing for growing teams. Less suited for large enterprise environments with complex compliance requirements.
8. SolarWinds Patch Manager
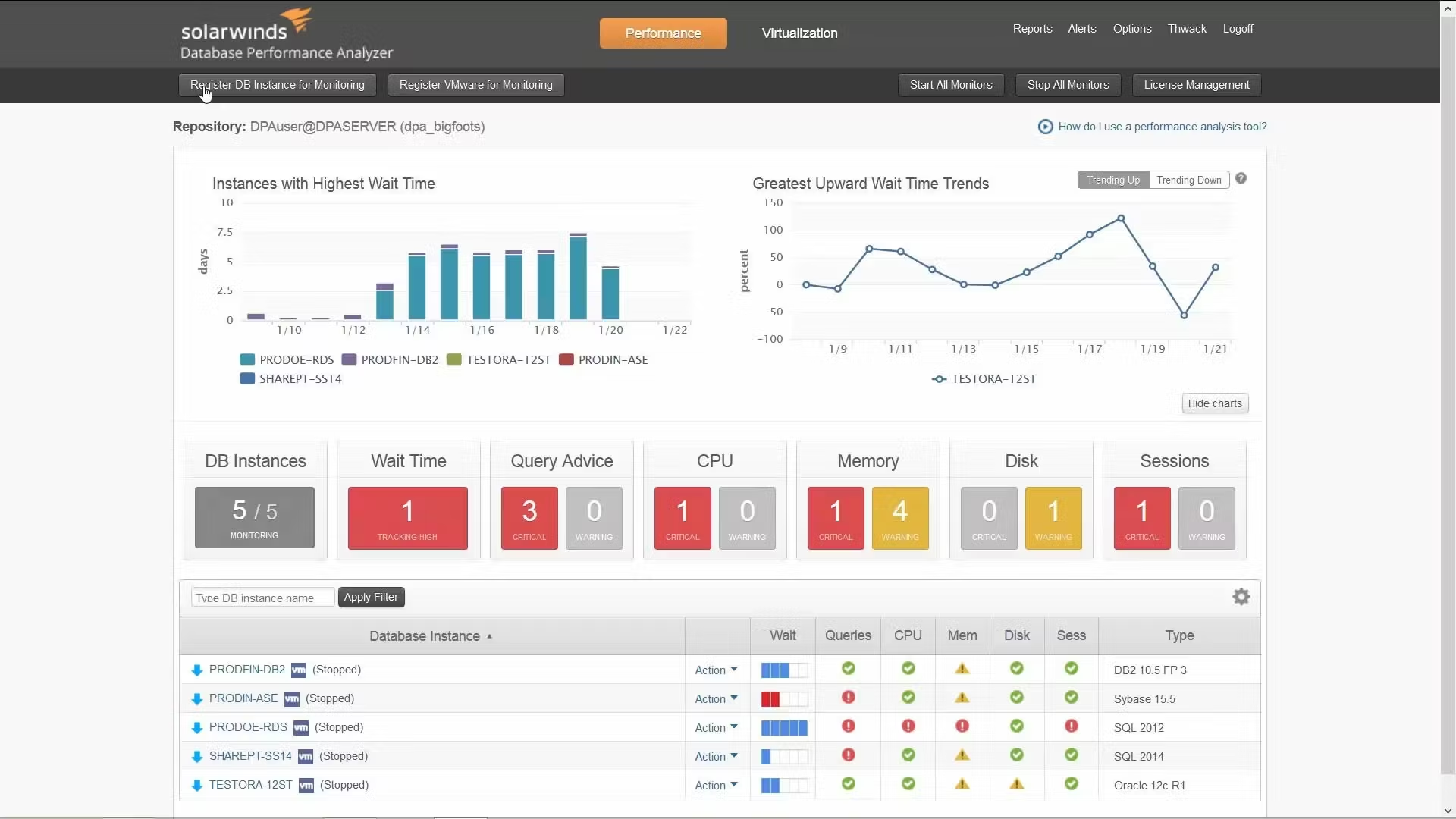
A long-standing enterprise patch management solution with strong WSUS integration and detailed reporting. Well-suited for organizations heavily invested in the Microsoft ecosystem. Remote patching for off-network devices requires additional configuration.
Open Source Patch Management Tools
9. WSUS (Windows Server Update Services)

Microsoft’s free patch distribution service for Windows environments. WSUS is widely deployed but requires significant manual configuration, on-premises infrastructure, and does not cover third-party applications natively. Community extensions exist but add operational complexity.
10. Opsi
An open source client management system for Linux and Windows environments. Opsi supports software distribution, OS deployment, and patch management. Requires technical expertise to configure and maintain.
11. Ansible

Ansible is a configuration management and automation platform commonly adapted for patch automation workflows. Teams write playbooks to apply updates across server fleets. Powerful in engineering-led environments but not a turnkey patch management solution.
12. SaltStack

Similar to Ansible, SaltStack enables policy-driven configuration management including patch automation. It scales well in large infrastructure environments but requires dedicated engineering resources to operate effectively.
Important: Open source patch management tools are not inherently secure and can be misconfigured or exploited. Without dedicated vendor support, security updates for the tooling itself may be delayed, creating new risk in your remediation infrastructure.
Patch Management Software Comparison Table
|
Tool |
Cross-OS Support |
Third-Party Patching |
Automation |
Remote Device Support |
Deployment Model |
Ease of Use |
|
Kitecyber |
Windows, macOS, Linux |
Broad (500+ apps) |
High |
Native |
Cloud-native |
High |
|
Microsoft Intune |
Windows-focused |
Limited |
Medium |
Good |
Cloud |
Medium |
|
ManageEngine |
Windows, macOS, Linux |
Strong |
High |
Good |
Cloud / On-prem |
Medium |
|
Automox |
Windows, macOS, Linux |
Good |
High |
Native |
Cloud-native |
High |
|
Ivanti |
Windows, macOS, Linux |
Strong |
High |
Good |
Cloud / On-prem |
Medium |
|
NinjaOne |
Windows, macOS |
Good |
Medium-High |
Good |
Cloud |
High |
|
Atera |
Windows, macOS |
Good |
Medium |
Good |
Cloud |
High |
|
SolarWinds |
Windows-focused |
Limited |
Medium |
Limited |
On-prem / Hybrid |
Medium |
|
WSUS |
Windows only |
None |
Low |
Poor |
On-premises |
Low |
|
Ansible |
Linux-focused |
Custom |
High |
Requires config |
Self-hosted |
Low |
How Kitecyber Patch Management Works
Endpoint-First Architecture
Kitecyber deploys a lightweight agent to each endpoint that provides continuous visibility into installed software versions, missing patches, and active vulnerabilities. The agent communicates directly with the cloud management platform without requiring on-premises infrastructure or VPN dependency.
Unified Visibility Across Devices
A single dashboard surfaces patch status across every managed device, including remote laptops, virtual machines, and cloud workloads. Security teams see open CVEs, patch coverage percentages, compliance status, and risk exposure in one view.
Automated Patching Workflows
Policy templates define patching behavior by device group, OS, application category, and risk tier. Once configured, the platform executes patching workflows automatically during defined maintenance windows, handling download, staging, testing, and deployment without requiring manual steps.
Real-Time Compliance Tracking
Patch coverage data maps continuously to compliance frameworks. When a new CVE is disclosed and a patch becomes available, compliance dashboards update in real time to reflect current exposure. Audit reports are always current, not snapshots from last month’s scan.
Kitecyber Key Features
- Cross-OS Patching Windows, macOS, and Linux endpoints are managed from a single platform. No separate tools, no separate consoles, no coverage gaps by operating system.
- Third-Party Application Patching Kitecyber's catalog may cover 500+ third-party applications including browsers, productivity tools, developer utilities, and collaboration platforms. Third-party patching runs on the same automated schedule as OS patching.
- Risk-Based Prioritization The platform weighs CVSS scores against active exploit data, threat intelligence feeds, and asset criticality to surface the highest-priority patches first. Teams spend remediation effort where it reduces the most risk.
- Remote Workforce Support Cloud-native delivery patches remote devices without requiring VPN. Whether your team is in an office or distributed across time zones, all devices stay current on the same schedule.
- Unified Security and Patching Visibility Patch management in Kitecyber is not a standalone module. It connects with the broader endpoint security posture, so patch gaps appear in the same context as misconfiguration risks, policy violations, and threat detections.
Use Cases
Remote Workforce Patching
A 500-person company with 80% remote workforce struggled to maintain patch coverage across laptops that connected to corporate VPN infrequently. After deploying Kitecyber, cloud-native patching brought all devices to full coverage within 30 days without requiring any VPN sessions.
Ransomware Prevention
Organizations using risk-based patch prioritization can identify CVEs actively used in ransomware campaigns and accelerate remediation for those specific vulnerabilities, reducing exposure to campaigns that rely on known, patchable flaws.
Compliance Enforcement
Regulated industries under PCI DSS and HIPAA need evidence of timely patching. Kitecyber’s compliance reporting generates audit-ready documentation that maps patch deployment dates to specific CVE disclosures and regulatory timelines.
IT Automation
IT teams using Kitecyber reduce manual patching tasks significantly. Automated patch policies, approval workflows, and deployment scheduling free up IT resources for higher-value work.
Deployment and Scalability
Cloud-Native from Day One
Kitecyber requires no on-premises infrastructure. There are no servers to provision, no databases to manage, and no update cycles for the platform itself. The management console is accessible from any browser.
Fast Rollout
Agent deployment can be completed via Group Policy, MDM platforms, or scripted installers. Enterprises can move from deployment to full patching coverage in days, not months.
Scales Without Complexity
Whether you manage 200 endpoints or 20,000, the platform scales linearly. Multi-tenant support allows MSPs and enterprise teams managing subsidiary organizations to operate from a single console.
Proof and Differentiation
- Reduced Patching Time Organizations moving from manual or semi-automated patching to Kitecyber may see time spent on patching operations decrease substantially in the first quarter of deployment. Policy automation removes the per-device manual effort that makes large-scale patching unsustainable.
- Lower TCO Consolidating OS patching, third-party patching, vulnerability scanning, and compliance reporting into one platform can reduce licensing costs and tool overlap compared to running separate point solutions for each function.
- Unified Security Approach Patch management that lives inside a broader endpoint security platform provides context that standalone tools cannot. A vulnerability flagged by the scanner, matched to an available patch, and remediated through the same platform closes the loop in a way that disconnected tools cannot.
See Kitecyber Patch Management in Action
Your endpoints are exposed right now. The CVEs that enabled last year's most damaging ransomware campaigns are still exploitable in environments with inconsistent patching. Kitecyber closes that gap automatically.
see how Kitecyber can bring full patch coverage to your environment in under 30 days.
With over a decade of experience steering cybersecurity initiatives, my core competencies lie in network architecture and security, essential in today's digital landscape. At Kitecyber, our mission resonates with my quest to tackle first-order cybersecurity challenges. My commitment to innovation and excellence, coupled with a strategic mindset, empowers our team to safeguard our industry's future against emerging threats.
Since co-founding Kitecyber, my focus has been on assembling a team of adept security researchers to address critical vulnerabilities and enhance our network and user security measures. Utilizing my expertise in the Internet Protocol Suite (TCP/IP) and Cybersecurity, we've championed the development of robust solutions to strengthen cyber defenses and operations.
Posts: 54
With over a decade of experience steering cybersecurity initiatives, my core competencies lie in network architecture and security, essential in today's digital landscape. At Kitecyber, our mission resonates with my quest to tackle first-order cybersecurity challenges. My commitment to innovation and excellence, coupled with a strategic mindset, empowers our team to safeguard our industry's future against emerging threats.
Since co-founding Kitecyber, my focus has been on assembling a team of adept security researchers to address critical vulnerabilities and enhance our network and user security measures. Utilizing my expertise in the Internet Protocol Suite (TCP/IP) and Cybersecurity, we've championed the development of robust solutions to strengthen cyber defenses and operations.
Posts: 54