Table Of Content
11 Best IT Security Management Software in 2026: Ranked, Tested, and Proven
-
February 25, 2026
-
The best IT security management software solves this by bringing device management, threat detection, compliance, and access control under one roof. No more patching together five different subscriptions. No more blind spots between your IT team and your security team.
This guide covers the 11 best IT and security management software platforms you can use right now in 2025. Each pick is evaluated on coverage, ease of use, scalability, and real value for money. Whether you are running a lean startup or managing hundreds of endpoints across a distributed workforce, one of these platforms will help you streamline your IT & security needs.
What Makes a Great IT and Security Management Platform?
- Unified visibility. You need a single dashboard that shows devices, user activity, network access, and compliance gaps at the same time. Switching between tabs to piece together your security posture costs time and introduces errors.
- Zero trust capability. Perimeter-based security no longer cuts it. Your software should verify every user and device before granting access, regardless of where they are connecting from.
- Automation. Repetitive tasks like patch deployment, policy enforcement, and compliance reporting should run without your team having to babysit them.
- Compliance readiness. If your industry falls under SOC 2, ISO 27001, HIPAA, or PCI-DSS, your platform should map controls automatically, not require a consultant to interpret them.
- Low total cost of ownership. Many platforms look affordable upfront but require multiple add-ons to achieve full coverage. Factor in the real cost of the complete stack.
1. Kitecyber: Best IT and Security Automation Software Overall
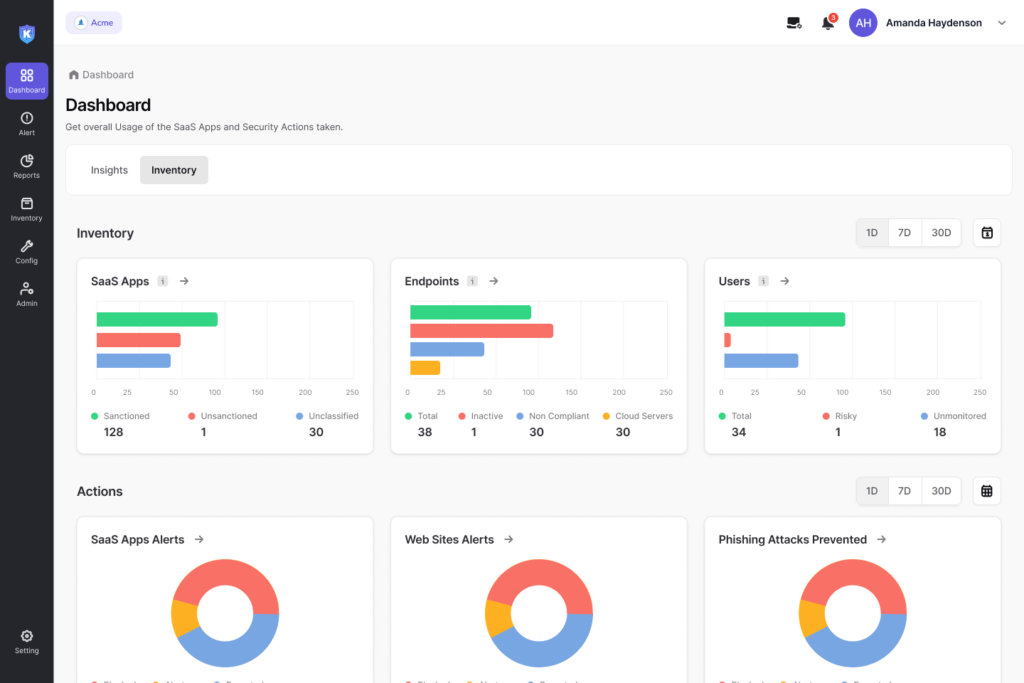
If you are running a modern distributed team and want one platform to handle device management, network security, Zero Trust access, data loss prevention, and compliance without managing cloud gateways or stacking multiple point solutions, Kitecyber is the one of the best IT Security Management Software to evaluate first.
Most organizations stack dozens of tools: data loss prevention, device management, access management, anti-phishing, network firewalls, and now GenAI filters. The result is high cost, high complexity, and fragmented data visibility. Kitecyber was built to collapse that stack into a single endpoint-based agent.
Unlike traditional SASE or SSE solutions that route all traffic through cloud gateways, Kitecyber moves network security to the endpoint and combines it with endpoint security. The solution runs entirely on endpoints with no cloud dependency. That means faster performance, no traffic bottlenecks, and no single point of failure.
Kitecyber covers UEM for Mac, Windows, and Linux devices; a next-gen secure web gateway with URL filtering and phishing protection; Zero Trust Network Access (ZTNA) as a VPN replacement; Data Loss Prevention (DLP) for data at rest and in transit; and SaaS discovery and governance. It also provides built-in compliance frameworks that map over 30 frameworks including SOC 2, HIPAA, ISO 27001, NIST, and more into device-level policies and continuous monitoring.
The platform also includes an industry-first, endpoint-based anti-phishing solution that detects and blocks attacks in real time within milliseconds. Modern SaaS applications often bypass traditional SSO logins, creating blind spots for device management and SaaS tracking. Kitecyber addresses this by instantly discovering all SaaS apps in use and offering precise access controls, including visibility of any open CVE’s against them.
2. ConnectWise: Best for Managed Service Providers
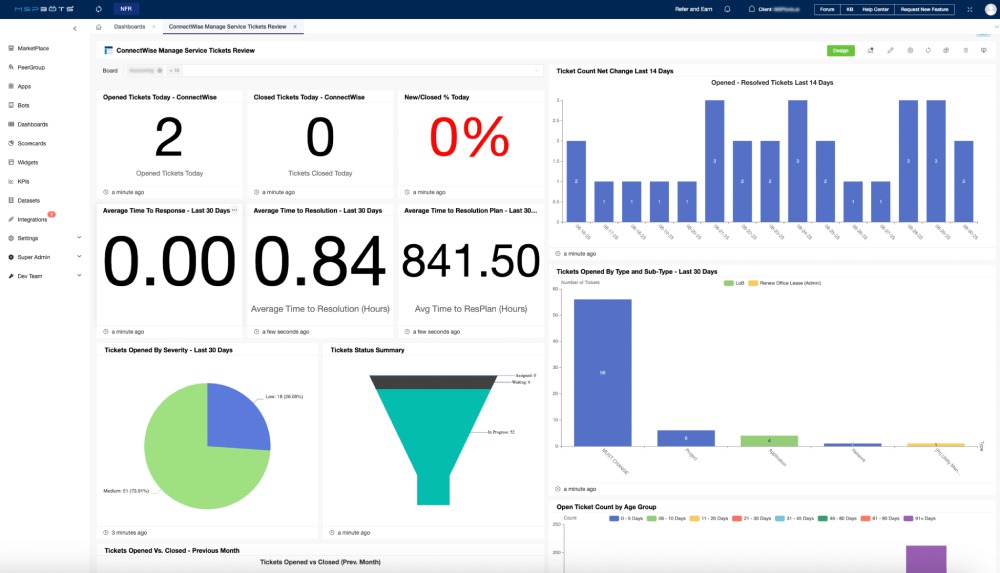
The ConnectWise suite combines service desk functions, asset and device oversight, remote monitoring, remote access, automation tools, and business management features. Its RMM component, ConnectWise Automate, gives technicians a scripting engine powerful enough to automate nearly any routine task. It includes over 500 out-of-the-box monitors and can perform asset discovery on any network with agent and agentless support. ConnectWise also includes a security module that helps with managing antivirus, anti-malware, email protection, and encryption, making it one of the few RMM platforms that starts to bridge the IT and security gap for MSPs serving small and mid-sized businesses.
The platform also handles time tracking, billing, agreements, and reporting tailored to MSP business models, so technicians and business managers can work from the same system.
Limitations: The depth and flexibility come with a steep learning curve and a complex setup process. ConnectWise uses quote-based pricing, which tends to be on the higher end, and it works best for technically skilled teams who require granular control over client environments.
Best for: MSPs managing multiple client environments who need automation-heavy tooling and are comfortable investing in setup and training time.
3. ManageEngine: Best Modular IT Management Suite

ManageEngine is a broad IT management platform that includes multiple products: ServiceDesk Plus for ITSM, Asset Explorer, Endpoint Central for device management and patching, and OpManager for network and server monitoring. Organizations use these components individually or together to handle tickets, maintain hardware and software records, oversee devices, and track infrastructure health.
Its Patch Manager Plus supports over 850 third-party applications, making it one of the most comprehensive patching solutions available. You get both on-premise and cloud deployment options, giving you flexibility that cloud-only platforms cannot match. The platform also includes network configuration management with real-time change tracking, compliance checks, and firmware vulnerability management.
ManageEngine’s pricing is competitive and predictable compared to many enterprise alternatives, making it a practical choice for midmarket organizations that want enterprise-level capabilities.
Limitations: Achieving a truly unified experience across ManageEngine's modular products may require purchasing multiple components, which can increase total cost and integration complexity over time. The interface on some modules also feels less modern than newer platforms.
Best for: Mid-to-large enterprises that want modular control over every IT function and are willing to invest in cross-module setup and integration.
4. SolarWinds: Best for Network Performance Monitoring
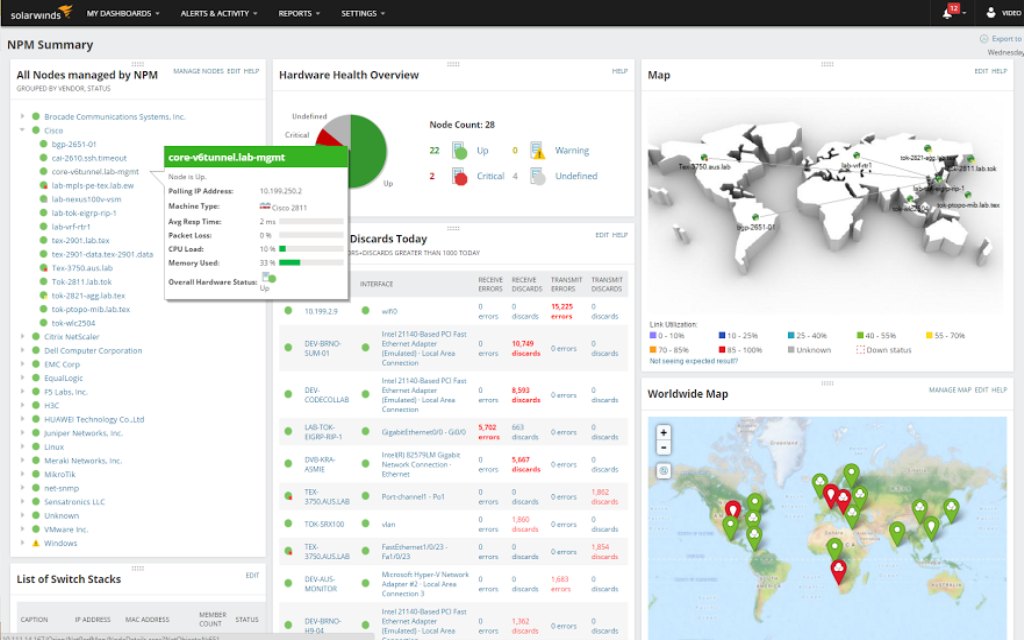
Its Orion platform consolidates multiple monitoring components into a single dashboard and offers advanced event correlation capabilities that allow IT teams to link performance events, understand root causes faster, and optimize incident response. SolarWinds also covers cloud visibility, database performance analysis, and application performance monitoring.
The platform’s assisted response feature identifies likely solutions from past cases, tracks ticket sentiment, and assigns work automatically, which can reduce the time technicians spend on routine triage.
Limitations: SolarWinds' element-based licensing can increase rapidly if not scoped properly. The setup and initial configuration also requires significant investment, and the interface can feel overwhelming without proper customization. The platform also carries reputational weight from its 2020 supply chain breach, which some enterprises still consider during vendor evaluation.
Best for: Enterprise IT operations teams focused on infrastructure monitoring, network performance, and hybrid cloud visibility who need a mature, established monitoring platform.
5. Kaseya VSA: Best for Endpoint Lifecycle Management
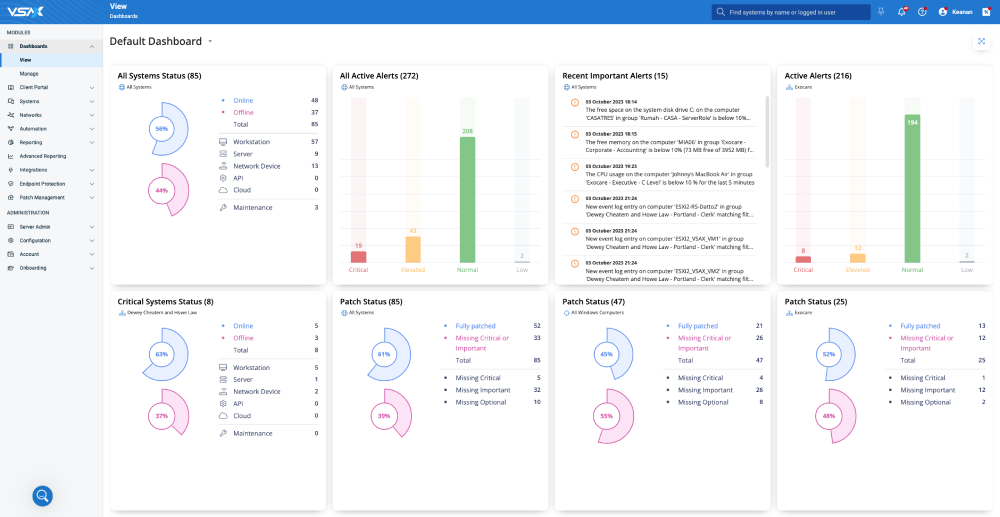
The platform offers policy-based automation with proactive remediation, software deployment automation, and patch and vulnerability management for Windows, Mac, and third-party applications. Kaseya expands through security and backup integrations with its broader portfolio, including Datto for backup and ID Agent for dark web monitoring, giving organizations a path toward a more complete security posture over time.
What makes Kaseya stand out is its scalability. Whether you are managing 50 endpoints or 50,000, the automation engine handles the load without requiring proportional headcount increases.
Limitations: Kaseya has faced criticism for its acquisition-heavy growth strategy, which can lead to inconsistent user experiences across integrated products. Pricing requires a direct quote and may be higher than expected for smaller organizations. The platform is also best known for IT management rather than native security capabilities.
Best for: IT teams and MSPs that need robust endpoint management and a clear path to building out a broader IT and security ecosystem over time.
6. NinjaOne: Best for Ease of Use

NinjaOne handles remote monitoring and management, patch management, remote access, backup, IT documentation, and endpoint security from a single cloud-based platform. Its mobile app gives technicians visibility and control even when they are away from their desk.
The platform integrates with security tools like Webroot, Bitdefender, and CrowdStrike, allowing teams to add threat detection on top of the management layer without switching platforms entirely.
NinjaOne is particularly strong for organizations that have tried more complex RMM platforms and found the learning curve to be a genuine obstacle to adoption. Teams that use it report fast onboarding and high daily satisfaction rates.
Limitations: NinjaOne depends on third-party integrations for deeper security coverage like ZTNA, DLP, or compliance reporting. Organizations with complex security requirements will likely need to supplement it with dedicated security tools.
Best for: SMBs and MSPs that prioritize a fast setup, a clean daily management experience, and a platform their team will actually enjoy using.
7. CrowdStrike Falcon: Best for Endpoint Threat Detection and Response
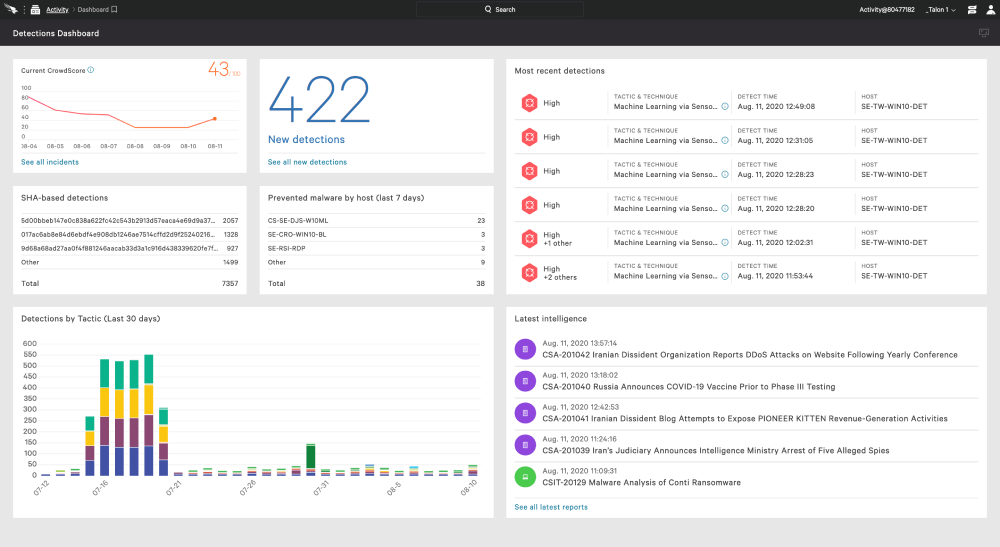
Falcon’s single lightweight agent collects endpoint telemetry and feeds it into CrowdStrike’s cloud-native Threat Graph, which processes over 10 trillion signals per week. The result is one of the fastest mean-time-to-detect capabilities in the industry.
The platform covers endpoint detection and response (EDR), next-gen antivirus, threat hunting, identity protection, and cloud security. Its Falcon Fusion SOAR module lets security teams build automated response playbooks without needing deep programming knowledge, reducing the analyst time required for repeated incident types.
Limitations: CrowdStrike is a premium product with premium pricing. It is designed primarily for security teams rather than IT management teams. Pairing it with an RMM or ITSM platform for full IT and security coverage is necessary for most organizations, which adds cost and integration work.
Best for: Mid-market to enterprise security teams that need best-in-class threat detection and can dedicate resources to managing a specialized security platform.
8. Microsoft Defender for Endpoint: Best for Microsoft-Centric Environments
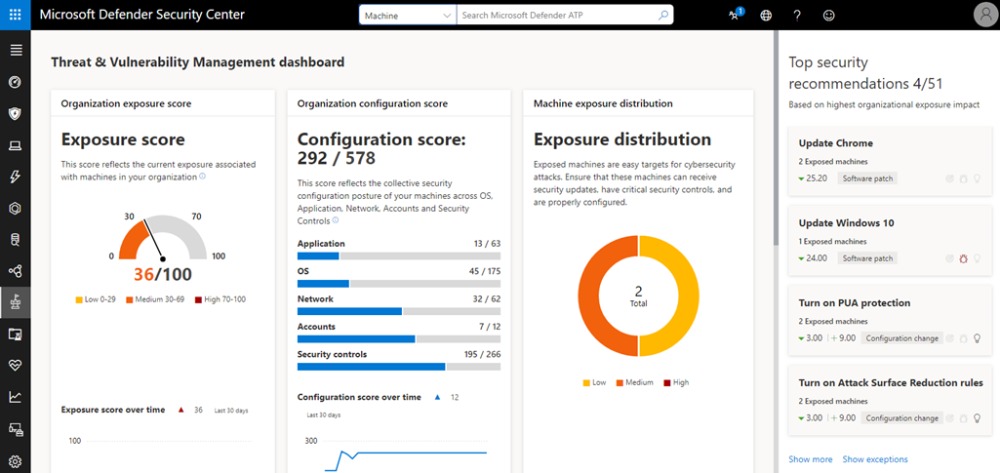
Defender for Endpoint provides threat and vulnerability management, attack surface reduction, behavioral-based detection, automated investigation and remediation, and integration with Microsoft Sentinel for SIEM capabilities. It also supports macOS, Linux, iOS, and Android, making cross-platform coverage possible within the Microsoft ecosystem.
The platform’s integration with Microsoft Intune for device management and Azure Active Directory for identity management allows organizations to combine endpoint management with endpoint security in a way that feels native and cohesive rather than bolted together.
Limitations: Defender for Endpoint is deeply optimized for Microsoft environments. Organizations with significant non-Microsoft infrastructure may find coverage gaps. Getting the most out of the platform also requires expertise in Microsoft's licensing tiers, which can be complex and change frequently.
Best for: Organizations already invested in the Microsoft ecosystem who want to maximize the security coverage from their existing licensing before adding new vendors.
9. Palo Alto Networks Cortex XSIAM: Best for AI-Driven Security Operations
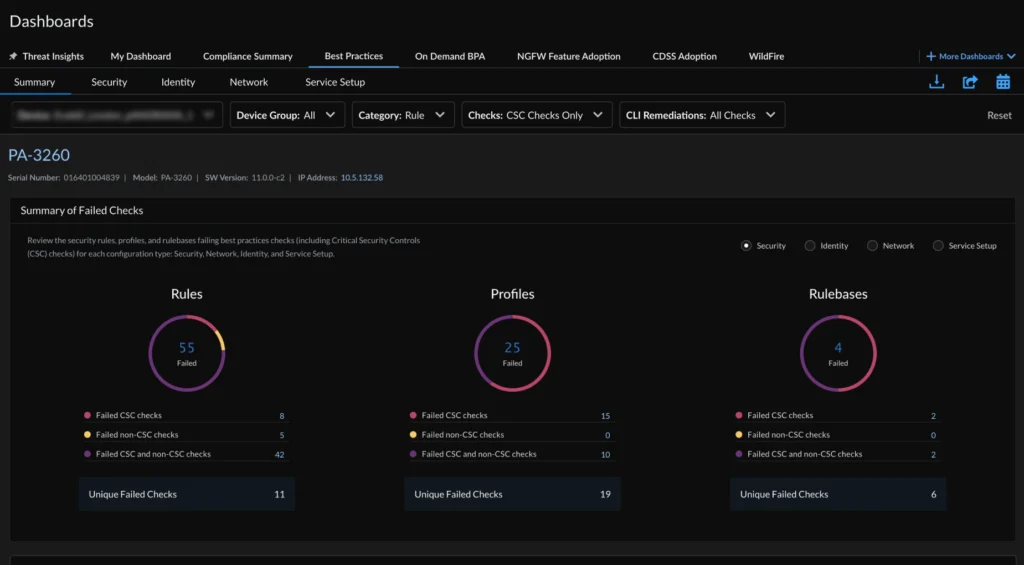
The platform ingests data from across your environment, including endpoints, network devices, cloud services, and identity providers, and uses machine learning to correlate alerts, detect threats, and automate responses. Cortex XSIAM reduces alert volume significantly by correlating what would normally be dozens of individual alerts into a single actionable incident.
For security operations teams dealing with alert fatigue, that reduction alone could justify the investment. The platform also includes threat intelligence from Unit 42, Palo Alto’s research arm, which gives your SOC access to current threat data that is continuously updated based on global attack patterns.
Limitations: Cortex XSIAM is built for organizations with mature security operations teams. It requires proper data integration and tuning to deliver its full value. Smaller organizations without a dedicated SOC may not see the return on what is a significant investment.
Best for: Enterprise security operations teams looking to modernize their SOC and reduce analyst burnout from high-volume, low-signal alerts.
10. Freshservice: Best IT Service Management for Growing Teams
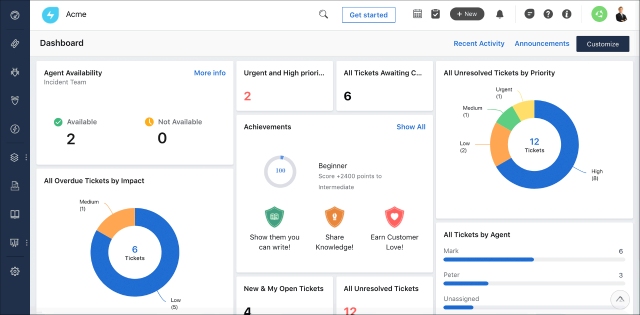
Freshservice brings together service management, asset tracking, and operational oversight. The suite covers request handling, incident response, change coordination, and problem management while also offering tools for IT asset management, IT operations management, and enterprise service management. Its AI-powered virtual agent handles routine employee requests automatically, freeing your team for work that requires human judgment.
The platform also supports workflows for change approval, risk assessment, and rollback planning, giving IT teams a structured way to manage infrastructure changes without creating unnecessary risk.
Limitations: Freshservice is strong on ITSM but does not offer native endpoint security, threat detection, or compliance management. It works best as one part of a broader IT and security stack rather than a standalone security solution.
Best for: Growing IT teams that want a modern, user-friendly service desk with solid asset management, AI automation, and room to scale without a painful implementation process.
11. Qualys: Best for Vulnerability Management and Compliance

The platform continuously scans your assets, whether they are on-premises, in the cloud, or remote endpoints, and delivers risk-scored vulnerability data that your team can act on immediately. Qualys also maps findings to compliance frameworks like PCI-DSS, HIPAA, and CIS Controls, reducing the manual work involved in audit preparation.
Its Policy Compliance module monitors configurations across your environment and flags deviations automatically, which is particularly valuable for organizations in regulated industries where continuous compliance monitoring is a requirement rather than an option.
Limitations: Qualys focuses on vulnerability and compliance management rather than IT management or day-to-day endpoint oversight. You will need a separate RMM or endpoint management solution alongside it. The interface can also feel dated compared to newer entrants in the security space.
Best for: Security and compliance teams in regulated industries who need continuous vulnerability scanning, detailed risk prioritization, and audit-ready compliance reporting.
How These 11 Platforms Compare at a Glance
|
Platform |
Primary Strength |
Best For |
|
Kitecyber |
Unified IT, security, and compliance |
SMB to mid-market, remote teams |
|
ConnectWise |
MSP operations and automation |
Managed service providers |
|
ManageEngine |
Modular IT management suite |
Mid to large enterprise |
|
SolarWinds |
Network performance monitoring |
Enterprise IT operations |
|
Kaseya VSA |
Endpoint lifecycle management |
IT teams and MSPs |
|
NinjaOne |
Ease of use and RMM |
SMBs and MSPs |
|
CrowdStrike Falcon |
Endpoint threat detection |
Enterprise security teams |
|
Microsoft Defender |
Microsoft-native endpoint security |
Microsoft-centric organizations |
|
Cortex XSIAM |
AI-driven security operations |
Enterprise SOC teams |
|
Freshservice |
IT service management |
Growing IT teams |
|
Qualys |
Vulnerability management |
Regulated industry security teams |
The Biggest Mistake Teams Make When Choosing IT Security Software
The smarter approach is to start with a platform that covers the majority of your use cases natively. Fewer integrations means fewer gaps. Fewer gaps means fewer incidents. And fewer incidents means your team spends time on strategic work instead of patching holes that a unified platform would have closed automatically.
One organization that adopted Kitecyber as its unified IT, security, and compliance solution saved approximately 50% in overall cost compared to its previous tools while significantly improving security posture and compliance coverage. That is the kind of outcome a unified platform can deliver when it replaces a fragmented stack.
Final Recommendation: What’s the best IT Security Management Software?
If you need the most complete, single-platform solution for IT management, security, and compliance with the fastest path to deployment, start your evaluation with Kitecyber. Its unified endpoint-based architecture removes the complexity that most other platforms push onto your team, and its ability to cover UEM, ZTNA, SWG, DLP, and compliance from one agent makes it the most efficient option available for organizations that want to move fast without sacrificing coverage.
If you are an MSP with a large client base and need RMM-first capabilities, ConnectWise or NinjaOne will serve you well. If enterprise-grade threat detection is your primary concern, CrowdStrike Falcon or Cortex XSIAM deserve serious evaluation. And if compliance and vulnerability management are your focus, Qualys has the depth you need.
The right platform is the one that closes your biggest security gaps today while giving your team the visibility to prevent tomorrow’s threats. Do not wait for an incident to tell you which gaps you have.