Table Of Content
How to Unlock AI’s Full Potential in IT, Security, and Compliance
-
August 28, 2025
-
Summary: Discover top SSE vendors & solutions in 2025, along with the list of features, competitors, and major differentiation (USP) of each vendor.
Introduction
Artificial Intelligence is no longer experimental—it’s now the backbone of productivity. Organizations are embedding AI-powered tools to streamline workflows, automate tasks, and unlock cost savings at scale. Yet many security leaders still rely on fragmented IT, security, and compliance systems that generate complexity instead of clarity.
Legacy solutions—endpoint security, device management, compliance automation, or IT service management—force teams into silos. Each system demands its own expertise, budget, and oversight, creating inefficiency and leaving gaps in visibility. In an AI-driven world, this model is a bottleneck.
The real challenge isn’t just adopting AI—it’s ensuring your IT, security, and compliance infrastructure can keep up with it. The same intelligence driving productivity should also protect data, manage users, and enforce compliance—without adding friction.
Legacy solutions—endpoint security, device management, compliance automation, or IT service management—force teams into silos. Each system demands its own expertise, budget, and oversight, creating inefficiency and leaving gaps in visibility. In an AI-driven world, this model is a bottleneck.
The real challenge isn’t just adopting AI—it’s ensuring your IT, security, and compliance infrastructure can keep up with it. The same intelligence driving productivity should also protect data, manage users, and enforce compliance—without adding friction.
The Challenge for Security Leaders
Leaders under budget constraints face a dual tension:
- Efficiency vs. Risk — Deliver robust protection across endpoints, SaaS apps, and networks while keeping costs under control.
- Fragmentation vs. Productivity — Managing multiple point solutions leads to tool sprawl, operational bottlenecks, and wasted resources.
This fragmented approach limits AI’s potential to drive real business value.
A Smarter, Unified Approach
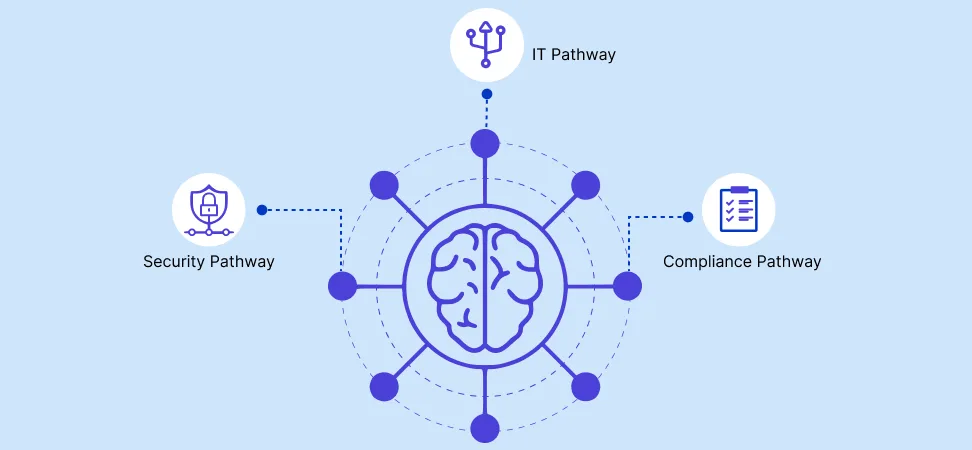
Kitecyber introduces a universal endpoint agent that brings AI and agentic automation to IT, Security, and Compliance:
- AI + Agentic Flows: Automates workflows like ticket resolution, onboarding/offboarding, and policy enforcement—freeing teams to focus on strategic priorities.
- Unified Security Layer: Consolidates IT, security, and compliance into a single platform—providing the right business context to drive intelligent automation, reducing complexity and cost.
- Continuous Monitoring & Enforcement: Integrates with cloud APIs and compliance vendors for always-on visibility, reporting, and automatic policy enforcement.
Additional Advantages:
- Security that never sleeps — whether offline, online, or in any location.
- Zero Trust on your device — without hairpinning or complex network detours.
- Compliant with data sovereignty and privacy laws — wherever your business operates.
By embedding intelligence directly into the endpoint, Kitecyber ensures your infrastructure doesn’t just keep pace with AI adoption—it thrives with it.
Benefits of a Modern Approach
With Kitecyber, security leaders can:
- Maximize Productivity: Automation frees teams from repetitive tasks so they can focus on strategic initiatives.
- Lower Costs: One agent replaces multiple point solutions, aligning with tight budgets.
- Simplify Compliance: Continuous enforcement reduces audit fatigue and ensures readiness.
- Strengthen Security: Unified visibility across devices, apps, and users lowers risk exposure.
Call to Action
The key to unlocking AI’s full potential isn’t just tools—it’s unified, intelligent IT, security, and compliance. Don’t let fragmented systems limit your outcomes.
With over a decade of experience steering cybersecurity initiatives, my core competencies lie in network architecture and security, essential in today's digital landscape. At Kitecyber, our mission resonates with my quest to tackle first-order cybersecurity challenges. My commitment to innovation and excellence, coupled with a strategic mindset, empowers our team to safeguard our industry's future against emerging threats.
Since co-founding Kitecyber, my focus has been on assembling a team of adept security researchers to address critical vulnerabilities and enhance our network and user security measures. Utilizing my expertise in the Internet Protocol Suite (TCP/IP) and Cybersecurity, we've championed the development of robust solutions to strengthen cyber defenses and operations.
Posts: 56
With over a decade of experience steering cybersecurity initiatives, my core competencies lie in network architecture and security, essential in today's digital landscape. At Kitecyber, our mission resonates with my quest to tackle first-order cybersecurity challenges. My commitment to innovation and excellence, coupled with a strategic mindset, empowers our team to safeguard our industry's future against emerging threats.
Since co-founding Kitecyber, my focus has been on assembling a team of adept security researchers to address critical vulnerabilities and enhance our network and user security measures. Utilizing my expertise in the Internet Protocol Suite (TCP/IP) and Cybersecurity, we've championed the development of robust solutions to strengthen cyber defenses and operations.
Posts: 56
Product
Solutions
Resources
Company
Comparison
Device Management
Data security
SaaS & Internet Security
Contact Us
- 691 S Milpitas Blvd, Ste 217, Milpitas, CA 95035


- We are SOC 2 Type II compliant